adminsatelliteRed Hat Satellite is an infrastructure management product specifically designed to keep Red Hat Enterprise Linux environments and other Red Hat infrastructure running efficiently, with security, and compliant with various standards.
In this lab, we will explore Satellite 6.5 by performing operations on the Satellite Server to demonstrate functionality and experience new features found in the 6.5 version.
In this lab, there is a Satellite, a Capsule, and two Red Hat Enterprise Linux 8 hosts. These are all virtual machines that are provided for your individual use. The following table gives more information about these systems and the next section will explain how to access these systems.
| System | SSH Nickname | Hostname | Notes |
|---|---|---|---|
| Satellite 6.5 Server | satellite | satellite65.example.com | A Satellite 6.5 server that we will be using in this lab |
| Satellite 6.5 Capsule | capsule | capsule.example.com | An external Capsule that has content synced |
| Host 1 | skylab | skylab.example.com | A Red Hat Enterprise Linux 8 host named 'skylab' that is registered directly to the Satellite |
| Host 2 | aqua | aqua.example.com | A Red Hat Enterprise Linux 8 host named 'aqua' that is registered to the external Capsule. |
Every attendee gets their own lab environment. The labs have already been deployed, to access your lab you need a unique Identifier (GUID) that will be part of the hostnames and URLs you need to access.
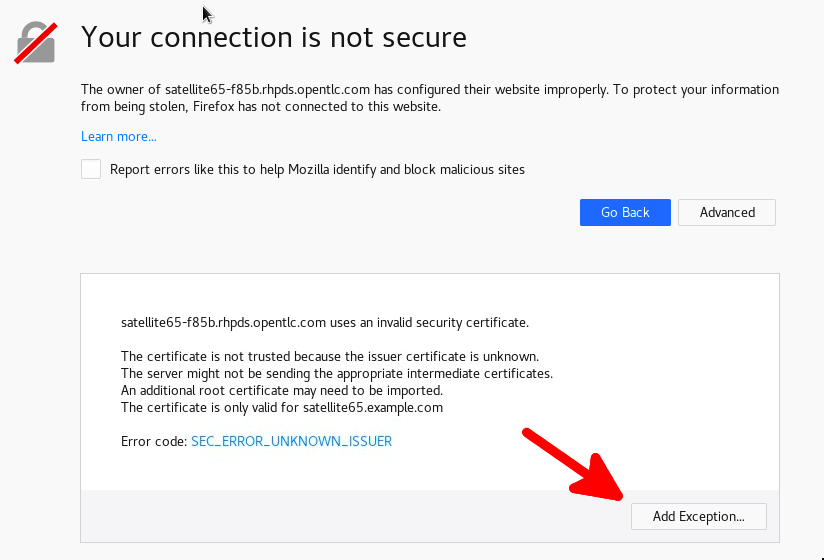
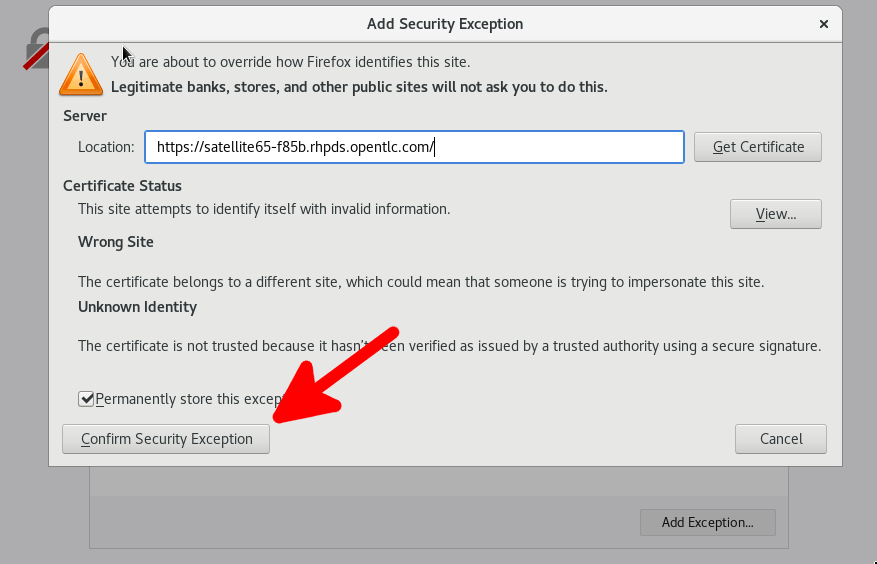
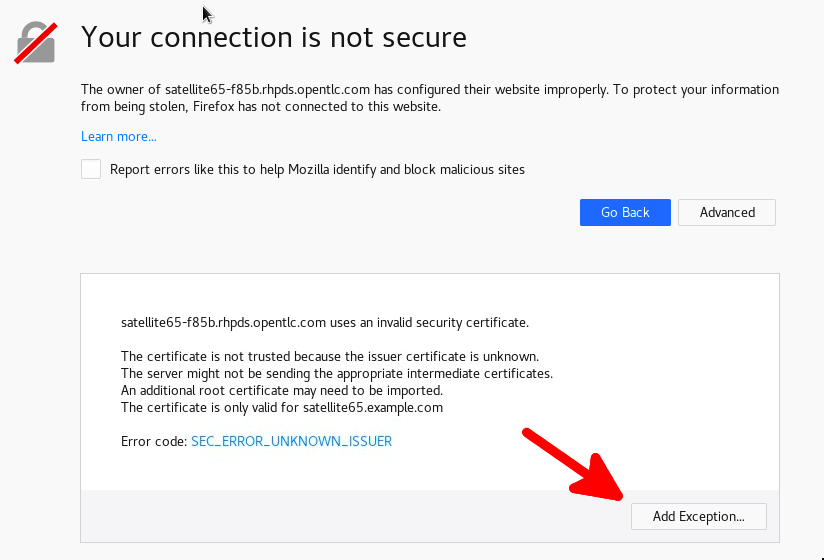
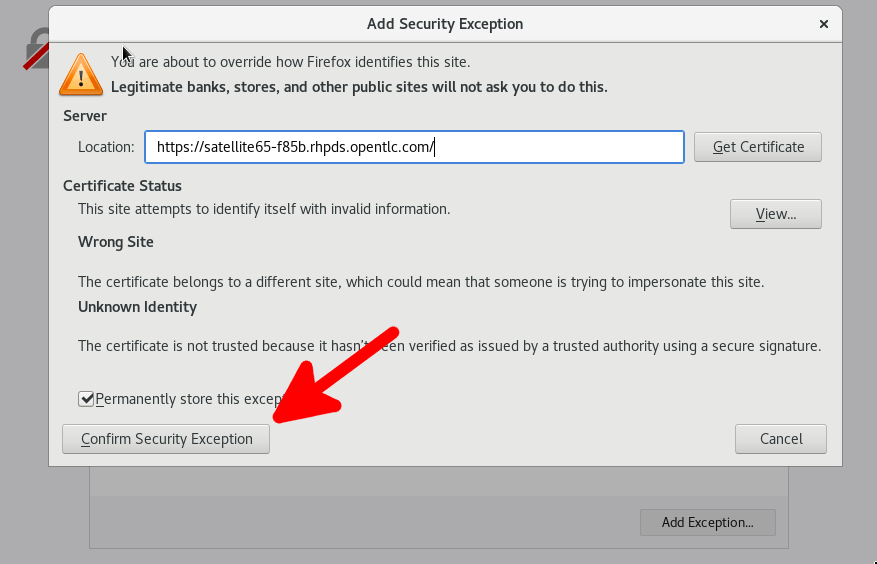
Hands On With Satellite 6.5 and enter spaceship for the activation keya1b2https://satellite65-<GUID>.rhpds.opentlc.com
adminsatellitebastion host, which is the entrypoint to the lab environment.lab-user:ssh lab-user@host-<GUID>.rhpds.opentlc.com
bastion host, you can access any of the virtual machines in the environment.ssh satellitessh capsulessh skylabssh aquassh lab-user@host-83d4.rhpds.opentlc.com
ssh satellite
skylab host:ssh skylab
https://satellite65-83d4.rhpds.opentlc.com
admin and password satelliteIf you have questions about accessing your lab environment, please reach out to a lab administrator to help
In this introductory section we will briefly familiarize ourselves with the user interface of Red Hat Satellite 6.5. The goal is to navigate to the major components and also view the pre-populated data for the lab. This section is optional for users with prior experience with Red Hat Satellite, feel free to continue to the next section.
When you log in, you are presented with a monitoring dashboard and a navigation system:
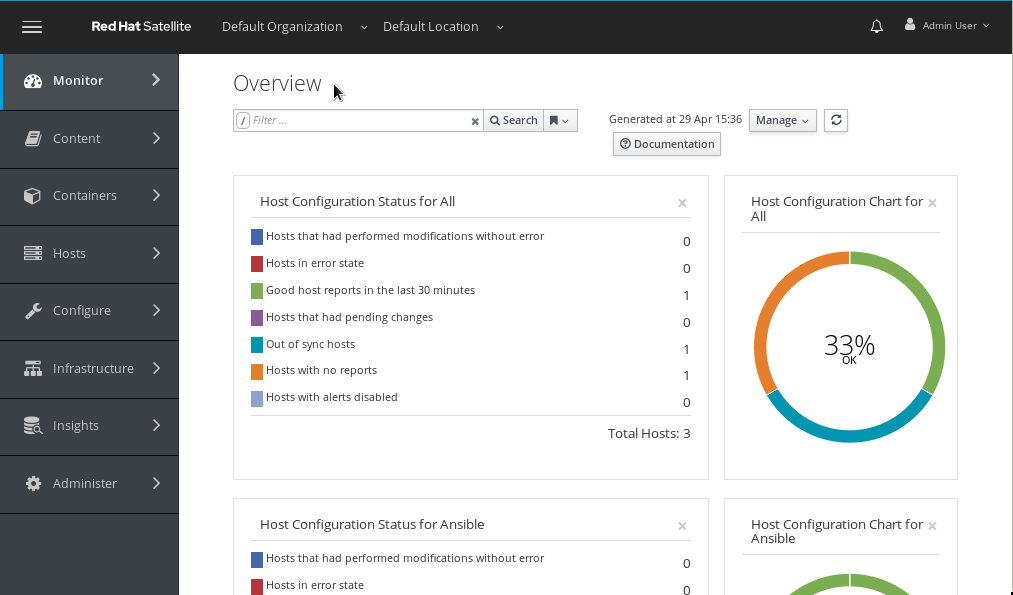
The main bar at the top of the page contains information on the currently managed Organization and Location. The bar also includes a notification drawer informing on recent system events and the user control on the right. Satellite 6 has a robust Role Based Access Control (RBAC) system which controls what actions users can take, and the resources (e.g. organizations) which they can access. For the sake of simplicity in this lab, we will use the Admin User account.
The vertical menu navigation on the left provides access to core functions of Red Hat Satellite including system provisioning, configuration and content management. Let's look closer at selected components:
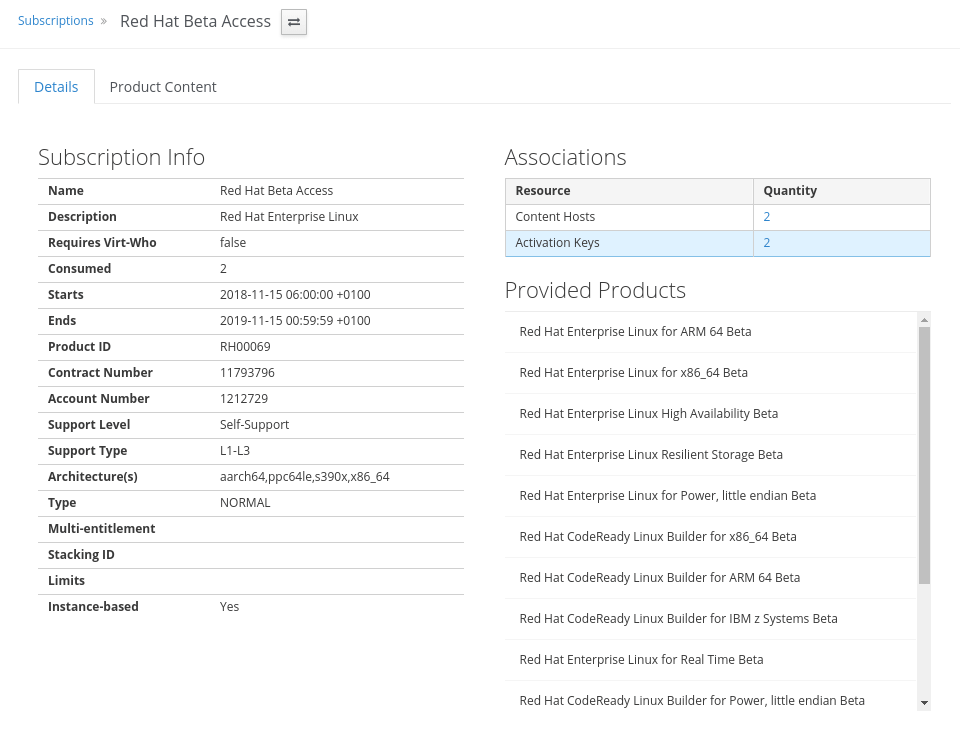
Navigate to Content > Subscriptions to view the list of subscriptions imported to the Satellite. These subscriptions enable synchronizing content from the Red Hat CDN. Click on Red Hat Beta Access to see the details of the subscription, including the provided products.
You will see SSL errors on this page as some communications are blocked to prevent modifying the manifest, these errors will not be present in normal Satellite installs, please ignore them for the duration of the lab
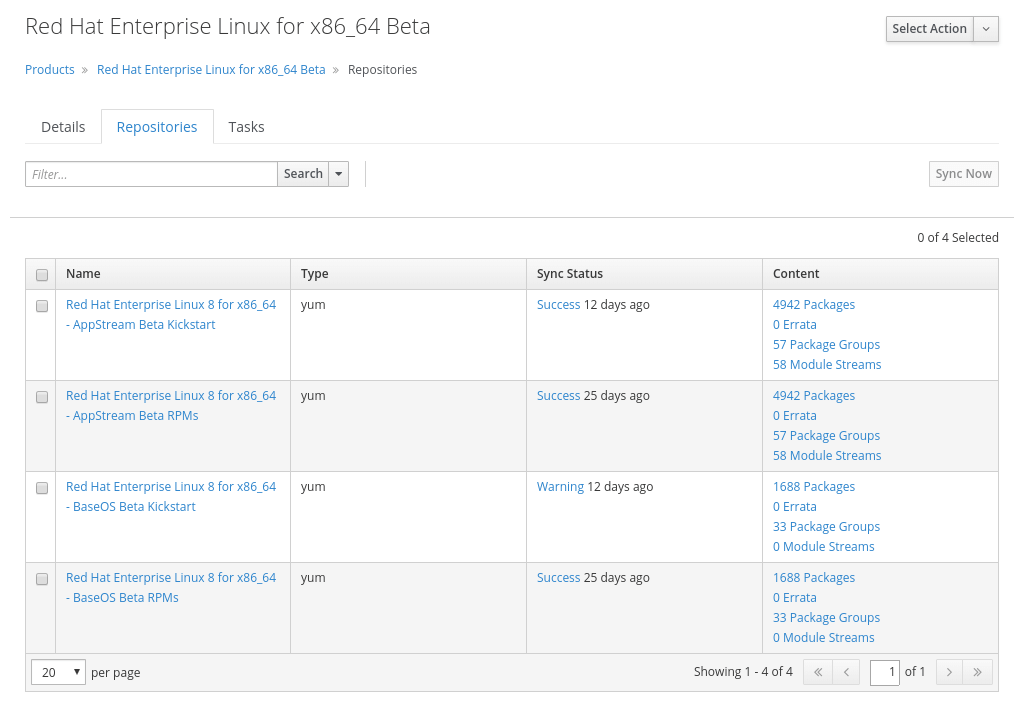
Navigate to Content > Products to observe the Products (collections of repositories) enabled by current subscriptions. Clicking on Red Hat Enterprise Linux for x86_64 Beta in the table than gives an overview of the associated repositories that you can explore further.
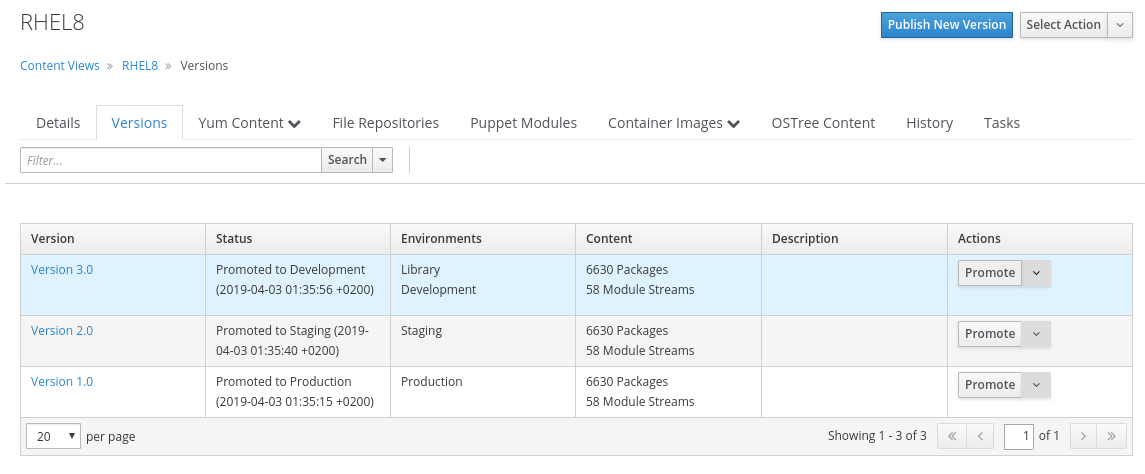
Navigate to Content > Content Views to see the currently existing Content Views (snapshots of content). Content Views can be promoted across Lifecycle Environments to provide a controlled deployment model where different machines are updated based on different schedules. For customers who do not wish to use content views, the Library contains a default content view with the latest version of all content. Click on RHEL8 to explore the Content View details.
Navigate to Configure > Host Groups to list the existing Host Groups that act as recipes for systems, describing how the system should be provisioned. When deploying the host into a location either on bare metal or in your hybrid cloud, the provisioning parameters are inherited from the Host Group. Click on RHEL8 to view the associated provisioning parameters for example the operating system (then click Cancel to leave the Host Group unchanged).
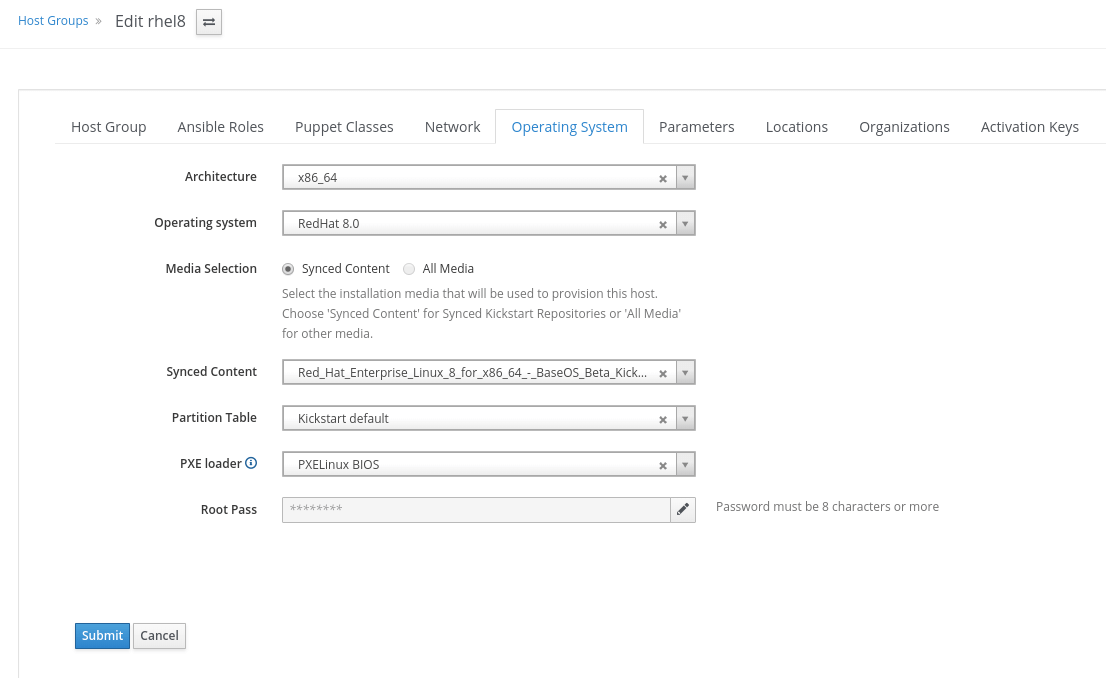
The provisioning parameters can be viewed under Hosts (e.g. Operating Systems) and Infrastructure (e.g. Domains or Subnets) menu items.
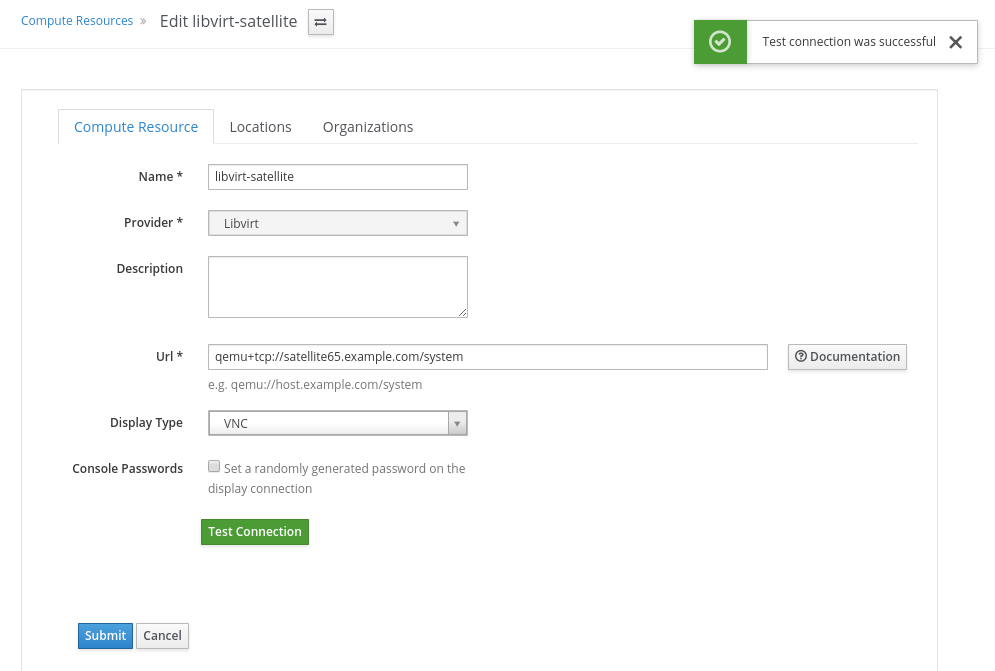
Navigate to Infrastructure > Compute Resources to view the Compute Resources available for provisioning. Satellite 6 supports the Hybrid Cloud model by allowing users to provision machines onto both bare metal machines and onto cloud fabrics such as EC2, OpenStack, RHEV-M, VMWare, etc. Compute Resources model the connection between Satellite 6 and the fabric. Click libvirt-satellite to view the existing Libvirt Compute Resource. To check if the Copmpute Resource is ready click Edit and then Test Connection (afterwards click Cancel to leave the Compute Resource unchanged).
Navigate to Hosts > All Hosts to see the list of all currently managed hosts. Click skylab.example.com to explore the host details.
We will now start the lab stories, which will guide you through performing operations with Satellite.
Satellite provides a tool called satellite-maintain that can help manage a Satellite system. We'll make sure all of our services are running before performing any operations on the Satellite.
satellite-maintain service status -b
[OK], please move to the next story of the labsatellite-maintain service restart
satellite-maintain service status -b
Satellite 6.5 enables the power and performance of Red Hat Enterprise Linux 8. With the inclusion of Red Hat Insights, your deployments will be kept secure and performant based on rich predictive analytics and the strong workflows of Satellite.
In this exercise, we will provision a new Red Hat Enterprise Linux 8 machine on a private network using a libvirt compute resource. The experience of using libvirt as a virtualization fabric is indicative of how Satellite 6 works when connected to Red Hat Enterprise Virtualization, VMWare, OpenStack, and EC2.
Hosts > Create Host to view the Create Host pageName field, enter summit-provisioned instead of the automatically generated nameHost tab select rhel8 from the Host Group drop-down list to inherit provisioning parameters from the predefined host group. You can navigate other tabs to view the populated parameters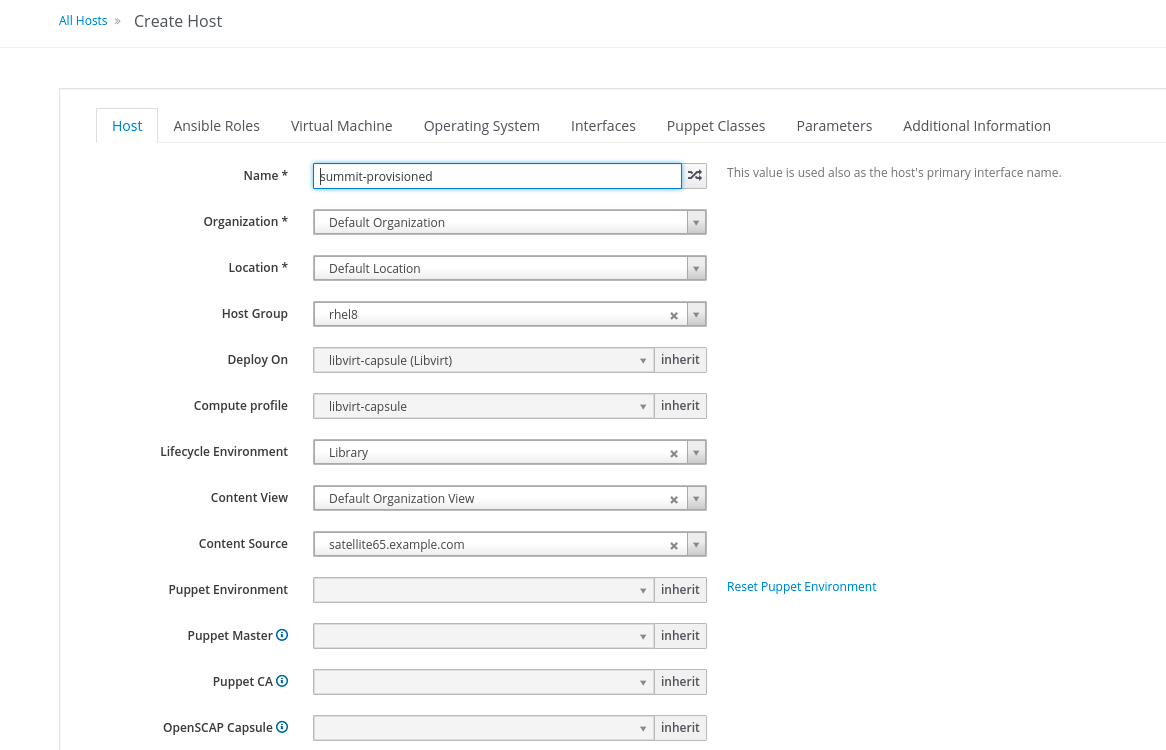
SubmitRed Hat Insights give you the ability to predict and prevent problems before they occur through ongoing, in-depth analysis of your infrastructure. Red Hat Insights now comes with all Red Hat Enterprise Linux subscriptions by default. This exercise shows you how to register a Red Hat Enterprise Linux 8 host to insight service via remote execution, observing actions, and fixing an SELinux issue using remote execution.
We will register our skylab host to Red Hat Insights using an Ansible playbook
Hosts > All Hostsskylab by clicking on Edit which is located under the action columnAnsible Roles tab, and select RedHatinsight.insight-client to move it to the Selected Items list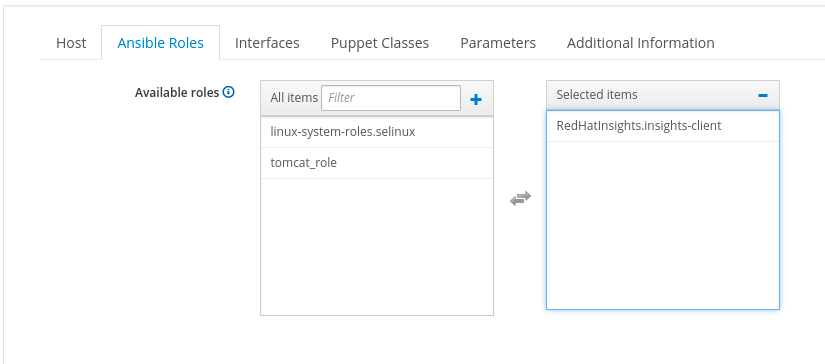
Submitskylab details page, click on Run Ansible Roles button in the upper right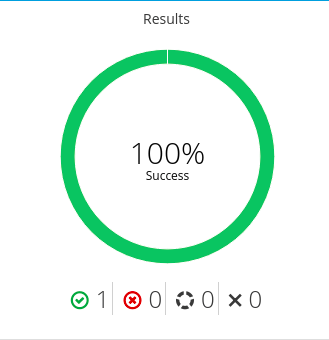
Insights > Overview and observe there is a registered host.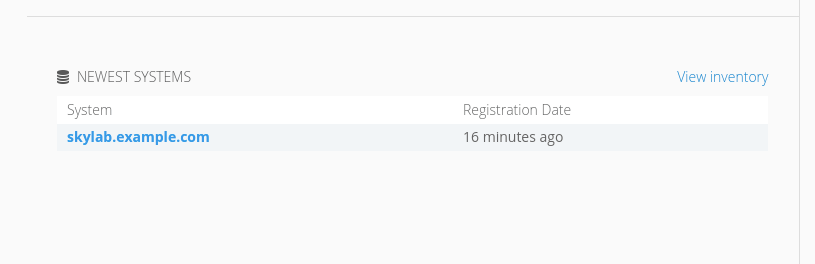
We will purposefully corrupt the SELinux config to show a fixable error in Insights
skylab host (remember you will need to ssh through the bastion host).setenforce 0. sed -i 's/SELINUXTYPE=targeted/SELINUXTYPE=shoulderror/' /etc/selinux/config
insights-client on the skylab host's terminal, this will create a new report and will upload it to insights service. Insights > Overview page, observe there is a new action with high severity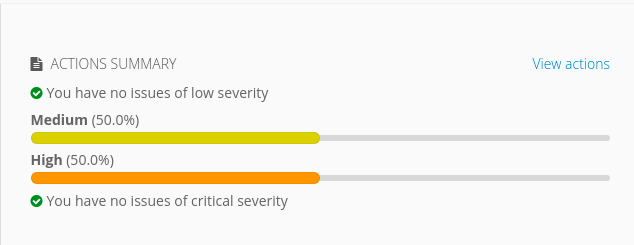
You will see a medium action here as well, this is something out of our control at the moment as it requires a change by the cloud provider. Please disregard this warning for the lab.
System will fail to boot when SELINUXTYPE is set improperly or the corresponding policy package is missing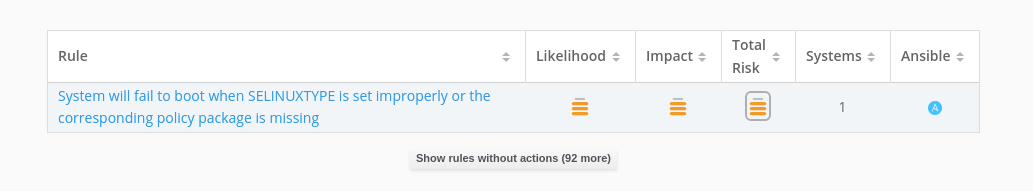
We will create a Red Hat Insights plan to correct the invalid SELinux config file. The fix will be applied through an Ansible playbook
Insights > Planner.Create a Plan, located on the upper right.Create new plan and give it the name SELinux config fix.skylab.example.com host.System will fail to boot when SELINUXTYPE is set improperly or the corresponding policy package is missing.Save.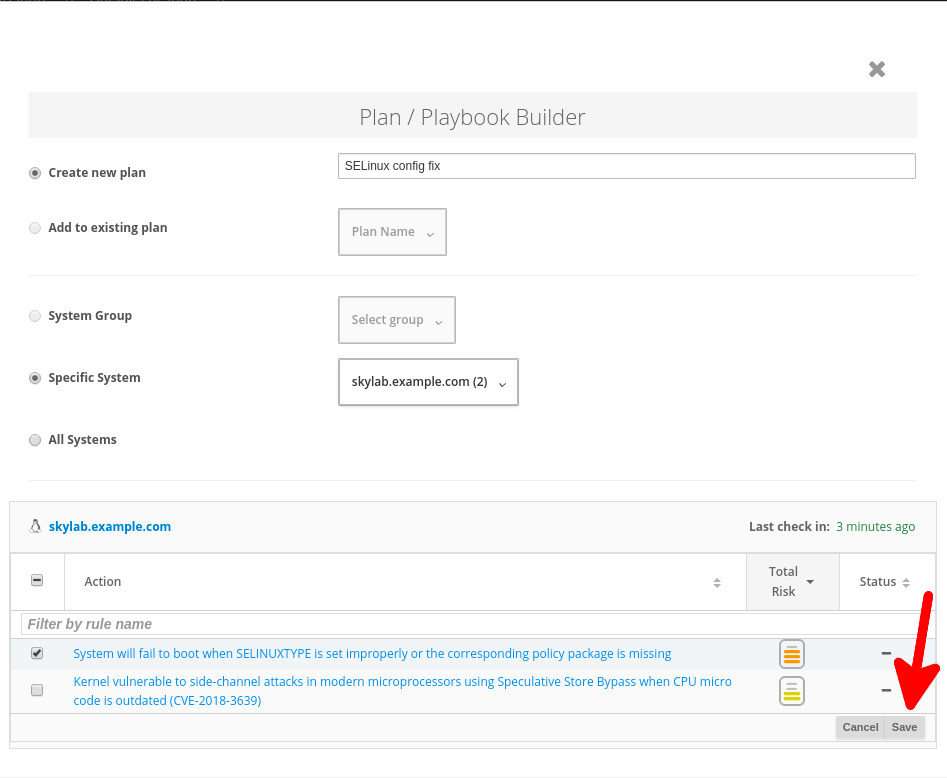
Run Playbook button.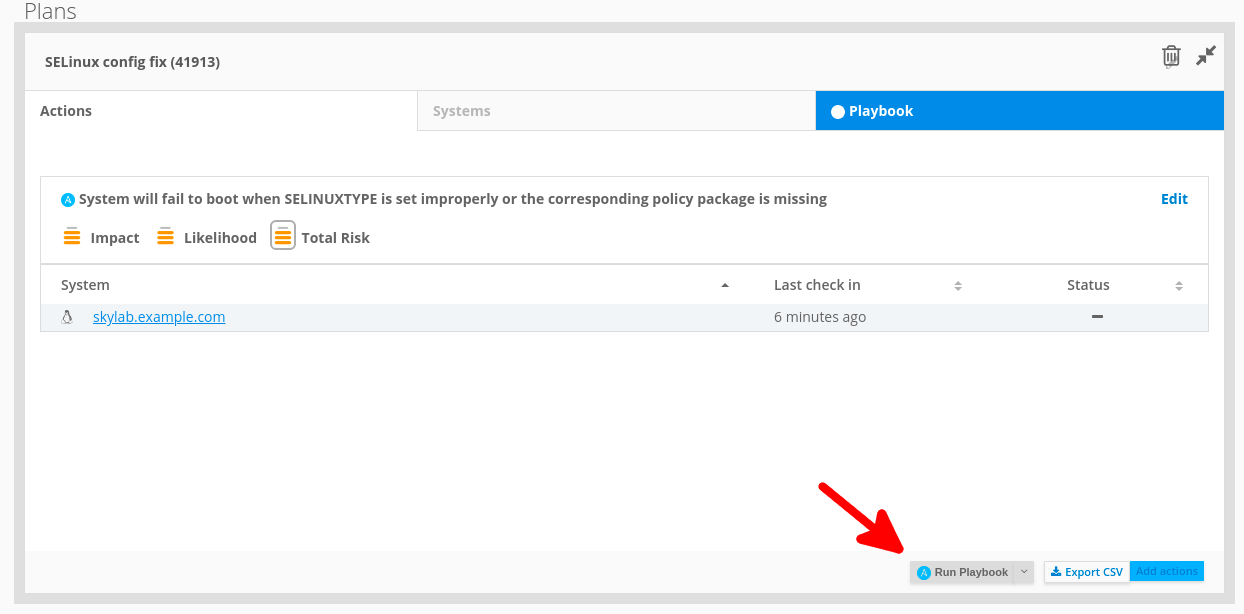
Insights > Overview, Notice no action appears as the SELinux issue has been fixed on the skylab host.Red Hat Enterprise Linux 8 allows for different versions of an application, such as Node.js, to be available to a system via modules. These Module Streams, often referred to as the "Application Stream" or AppStream for short, can be managed by Satellite 6.5. Users can view, enable, and install these modules to use a specific version range of an application even after updates. The errata workflows in Satellite 6.5 have also been enhanced to support Modules
Information about synced Module Streams is shown on the new Module Streams page
Content > Module Streams pagenodejs module using name = nodejs and repository = "Red Hat Enterprise Linux 8 for x86_64 - AppStream Beta RPMs"Satellite provides the ability to install Module Streams to a specific host. Assume you have an application that requires Node.js version 10 and you would like to make version 10 available to the system. Installing the nodejs module with stream 10 will allow your system to stay on Node.js 10 even as future versions are released.
Hosts > Content Hosts and then click on aqua.example.com to get to the content host details pageModule Streams tab and search name = nodejsnodejs stream 10, click the Actions menu and select Install to install the module stream on aqua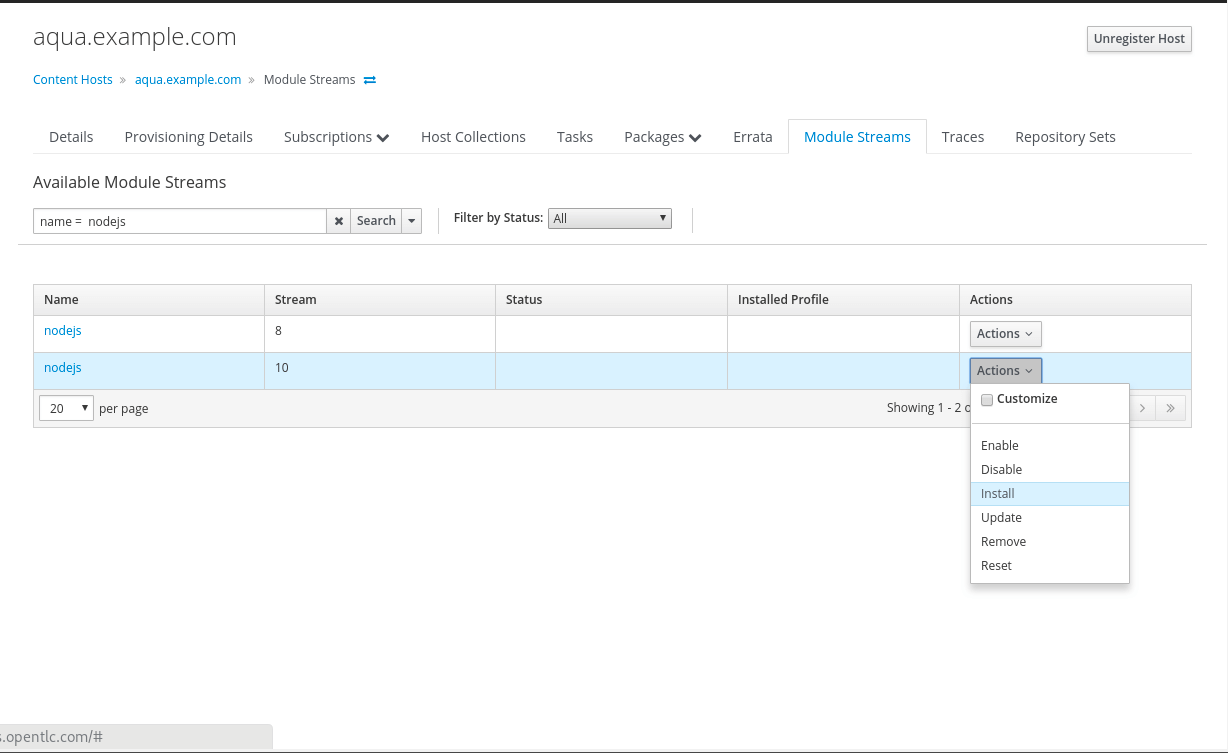
aqua.example.com in the hosts list at the bottom of the pageHosts > Content Hosts and click aqua.example.comModule Streams tabFilter by Status menu, select Installed. Notice the nodejs module stream is Enabled and Installed These actions can also be performed on multiple hosts with host collections or host bulk actions
The errata workflows in Satellite 6.5 have been enhanced to support Module Stream information. This exercise makes use of the new Reporting Engine framework in Satellite 6.5 to start the errata workflow.
Monitor > Report TemplatesApplicable Errata report template, click Generate.name = aqua.example.comsubmit this will prompt you to open or save the report file, you can open with a text editor for easy viewingaqua.example.com host, notice there is an applicable errata (it is in CSV format)Hosts > Content Hosts and then click on aqua.example.com to get to the content host details pagePackages > Installed tab, search for name = go-toolset to find the version of the package installed on the aqua hostgo-toolset-1.10.3-10.module+el8+2175+e66141eb.x86_64Errata tabRHSA-2018:2015 and click the dropdown caret next to Apply Selected and select via remote execution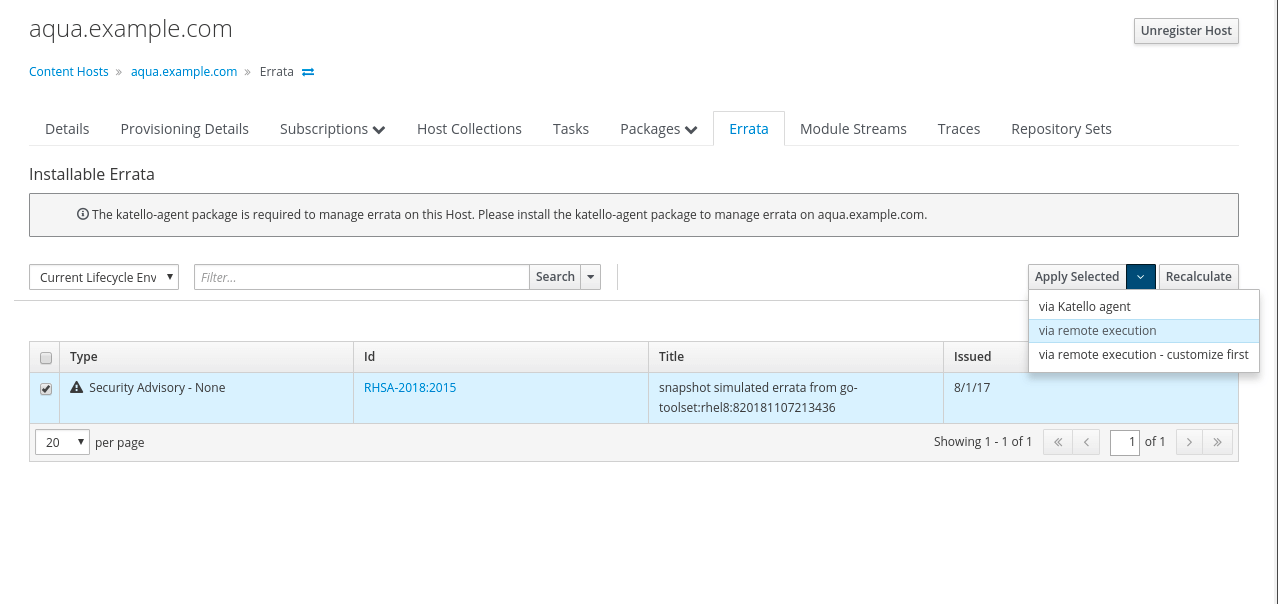
Hosts > Content Hosts and aqua.example.comErrata tab for host and verify there is no more installable errata.Packages > Installed tab, search for name = go-toolset to find the version of the package installedgo-toolset-1.10.3-12.module+el8+2195+f6fab0d5.x86_64Monitor > Report TemplatesGenerate on the Applicable Errata lineHosts filter box enter name = aqua.example.comSubmit and open the file.aqua host, notice there is no more applicable errata (the file will be blank)In the previous exercise, we used the built in report templates to view information about our hosts. Additional templates can be imported from the Foreman community repo or another git repository.
Hammer can be used to import report templates from a git repository. Also, templates can be filtered to just the ones you want to import. In this exercise, we'll import templates from the Foreman community repository
Monitor > Report Templates and notice there are four templates available, these are the default ones provided by Satellitehammer import-templates --prefix 'Community - ' \
--filter '.*statuses$' \
--branch ea0a9cdac724a49aa6d0b89108927c6cd2c7cc50 \
--organization 'Default Organization' \
--location 'Default Location'
After successful import the "Import finished" message is returned.
Report Templates page. You will see the Community - Host statuses template is imported.--filter flag.--repoSatellite can be used to manage system security and standards compliance. The skylab host is set up to use a Red Hat Enterprise Linux 8 OpenSCAP compliance profile that is tailored to a limited policy for demonstration purposes
Satellite can generate a Compliance Report for a host based on SCAP compliance profiles that have been uploaded to the Satellite. We'll generate a report for skylab.example.com
Hosts > All Hosts, and click on the skylab.example.com host.Schedule Remote Job dropdown menu and select Run OpenSCAP scan.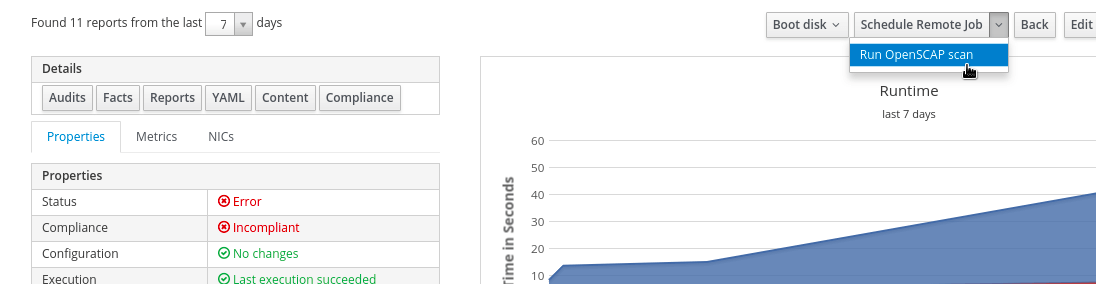
skylab.example.com, click Host DetailCompliance button Policy RHEL8 SCAP window, click RHEL8 SCAP latest report to view the compliance reportConfigure System Cryptography Policy has failed, see the summary for the command to fix by clicking the 'more details' caret next to the rule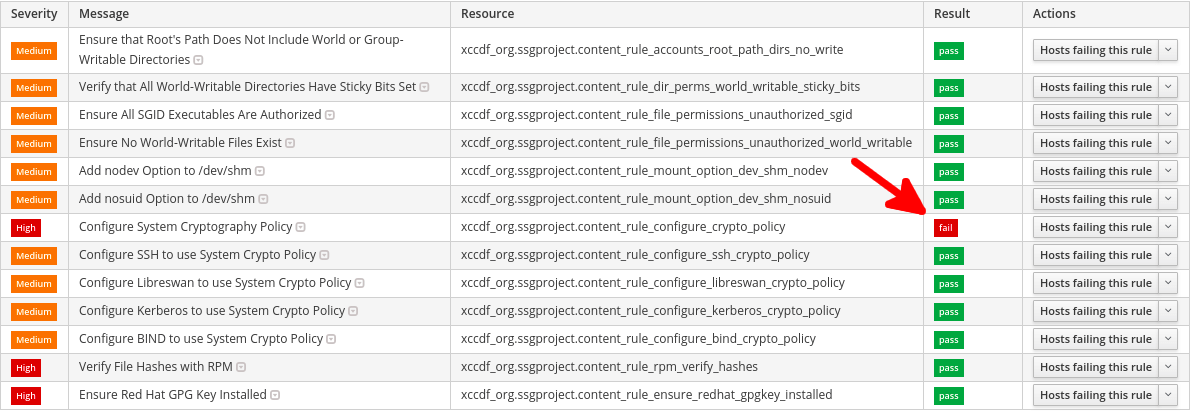
After a report has been generated for a host, we can fix those issues and generate a new report to ensure our system is compliant
Hosts > All Hosts and select the skylab.example.com hostSchedule Remote Job in the host detailssudo update-crypto-policies --set DEFAULT, this command will fix our compliance issue Submitskylab.example.com, click Host DetailSchedule Remote Job dropdown menu and select Run OpenSCAP scanskylab.example.com, click Host DetailCompliance button Policy RHEL8 SCAP window, click RHEL8 SCAP latest report to view the compliance reportSatellite 6.5 allows for custom cron-like syntax when creating Sync Plans for Products. This provides finer control over the frequency of content synchronization in Products. In this story, we will create a sync plan using custom cron syntax for our Tiny Product product
Content > Sync Plans, and click Create Sync PlanTiny Product Synccustom cron*/15 * * * *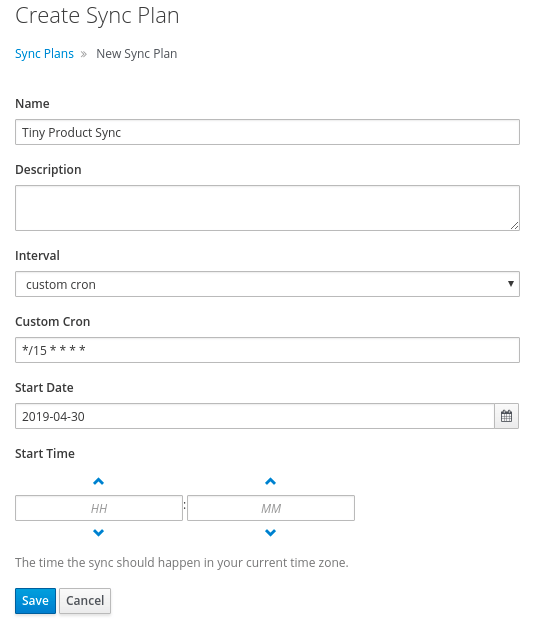
Save (you can leave the rest of the fields as the default values)Products tab for the newly created Sync PlanAdd tabTiny Product product by clicking the box next to its name and then clicking Add Selected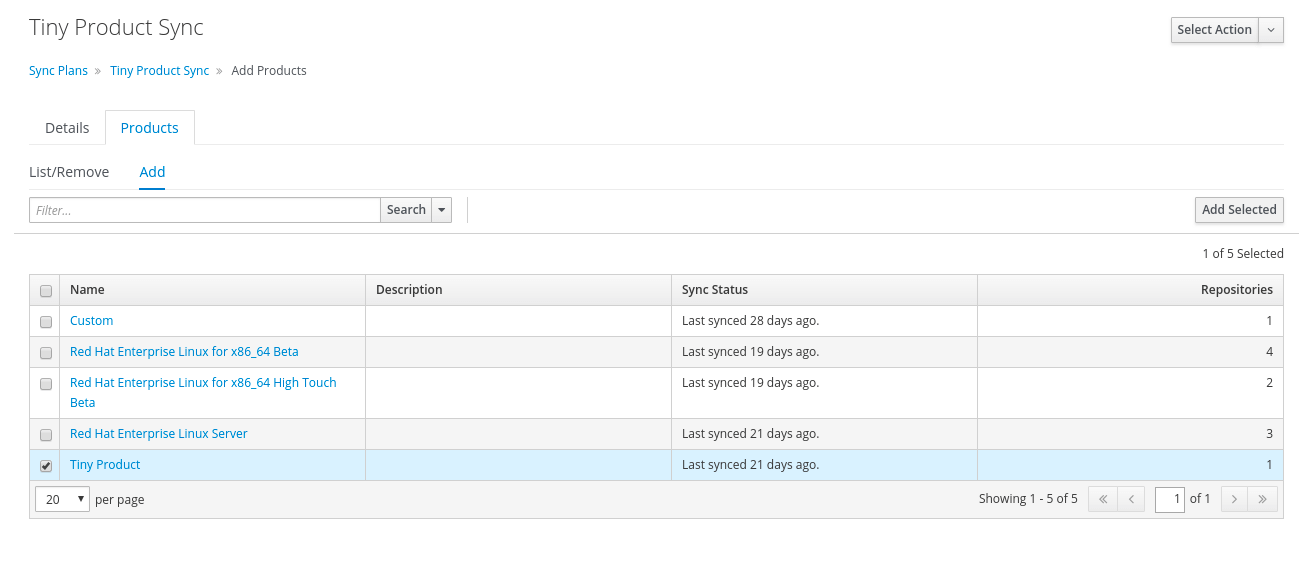
Monitor > Recurring LogicsContent > Product > Tiny Product > Tasks. Alternatively, navigate to Monitor > Tasks to find the sync taskSatellite 6.5 allows support for discovering container images through a registry. Additionally, you can require authentication in a lifecycle environment, meaning images in that environment will need the proper authentication to be pulled by a host.
A private Quay container registry is running on quay.example.com. Satellite can discover images there and add them as a Repository
Content > ProductsRepo Discovery buttonRepository Type field, select Container ImagesRegistry to Discover, select Custom and enter the URL quay.example.comRegistry Username field, enter summituserRegistry Password field, enter summitpasswordRegistry Search Parameter field, enter calipsoDiscoversummituser/calipsoCreate Selected
Run Repository CreationRepository Created linkSelect Action menu and select Sync NowSatellite can be configured to require authentication when using images that are in a Lifecycle Environment
Content > Lifecycle EnvironmentsProduction to navigate to the Production environment pageUnauthenticated Pull to No by clicking the field, unchecking the box, and clicking Save. This ensures authentication is needed to pull images from this environmentWe will create a Content View containing our discovered image and promote it to the Production Lifecycle Environment
Content > Content ViewsCreate New ViewRHEL8 container tagsSaveContainer Images > RepositoriesAdd tab, add summituser/calipso by selecting it and clicking Add RepositoriesPublish new version on the top right to publish the content viewSave to publish the Content View Version
Promote in the Version 1.0 rowContent View Version to the Production Lifecycle Environment, check the Production checkbox and click Promote VersionHosts > Content Hosts and then click on skylab.example.com to get to the content host details pageContent Host Content area, edit the associated content view to RHEL8 container tags and saveskylab host and run docker search satellite65.example.com/calipsodocker login satellite65.example.com and login with the username admin and password satellitedocker search satellite65.example.com/calipsoSatellite can set a naming pattern scheme for images in a particular Lifecycle environment
Content > Lifecycle EnvironmentsProduction to get to the details pageRegistry Name Pattern to be <%= repository.docker_upstream_name %> and save.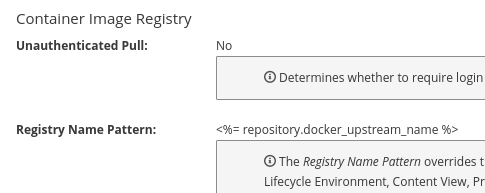
Important: you will need to wait 60 seconds for the the new registry name pattern to be indexed before pulling the image with the new name pattern
skylab host, run docker search satellite65.example.com/calipso againsummituser/calipso. This is the image in the production content viewdocker pull satellite65.example.com/summituser/calipsodocker imagesproduction/summituser/calipso?Red Hat Enterprise Linux 8 supports setting System Purpose parameters to identify the intended usage of the system. Satellite 6.5 leverages these parameters for auto-attaching subscriptions to registered Red Hat Enterprise Linux 8 hosts. This provides a way to define how the system is used and therefore improve how subscriptions are assigned and the machine is identified in the hosted application.
Hosts > All Hosts and select the summit-provisioned host that you create in the beginning of this lab during the Provision a Host on an External Compute Resource stepPower On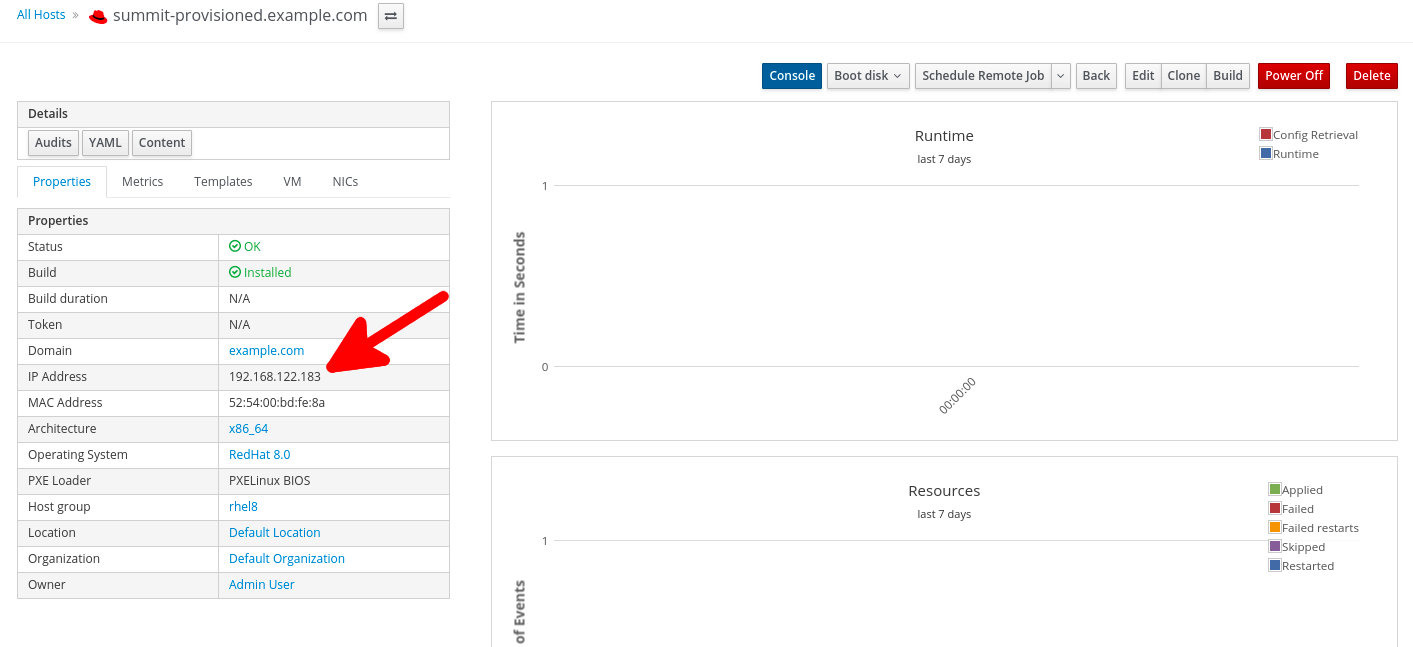
192.168.122.183 (replace this with the IP address found on the host details page) ssh capsule (on bastion host)ssh root@192.168.122.183 (on capsule)satelliteNote that provisioned hosts are usually registered to Satellite automatically at the end of the provisioning process (this is done by associating an Activation Key with required subscriptions to the Host Group used for provisioning). For demonstration purposes we will register the provisioned host manually:
cd ~
curl --insecure --output katello-ca-consumer-latest.noarch.rpm https://satellite65-<GUID>.rhpds.opentlc.com/pub/katello-ca-consumer-latest.noarch.rpm
yum install -y katello-ca-consumer-latest.noarch.rpm
subscription-manager register --org="Default_Organization" --environment="Library"
admin for the username and satellite for the passwordsubscription-manager repos to observe that system has no repositories available through subscriptions.syspurpose show to see there are no parameters currently specified for the host.In this section we will assign System Purpose parameters to the registered host. Satellite 6.5 supports setting these parameters in it's Web UI. Alternatively, you can use the syspurpose cli tool to set System Puropose in the host's terminal, such changes are then reflected in Satellite.
Hosts > Content Hosts and click summit-provisioned.example.com.Subscriptions tab and select Subscriptions to see that no subscriptions are currently attached.Details tab to see that the System Purpose Status is Mismatched. Set the system purpose parameters as follows:Self-Suport from the drop-down menu. Click Save.Production from the drop-down menu. Click Save.Red Hat Enterprise Linux Server from the drop-down menu. Click Save.Subscriptions tab and select Subscriptions to see that subscriptions have been attached based on the System Purpose settings (you may need to click Run Auto-attach and refresh page to see the changes).Details tab see that the system purpose status is now Matched.
summit-provisioned's terminal, run subscription-manager repos again to see the list of repositories enabled through the attached subscription. Also run syspurpose show to see the specified parameters.yum -y install vim
Satellite 6.5 delivers an enhanced Audits Page, which allows for viewing and searching actions performed by the Satellite
Modifying a template will show up with the template diff in its audit entry
Hosts > Provisioning Templatesname = epelepel template, click cloneSubmit to create the epel clone templateepel clone template, in the Provisioning Templates page search: name = "epel clone"https://dl.fedoraproject.org/pub/epel to http://mirrors.mit.edu/epel/repo_base = host_param('epel-repo-base') ? host_param('epel-repo-base') : 'http://mirrors.mit.edu/epel/'
Updated EPEL mirror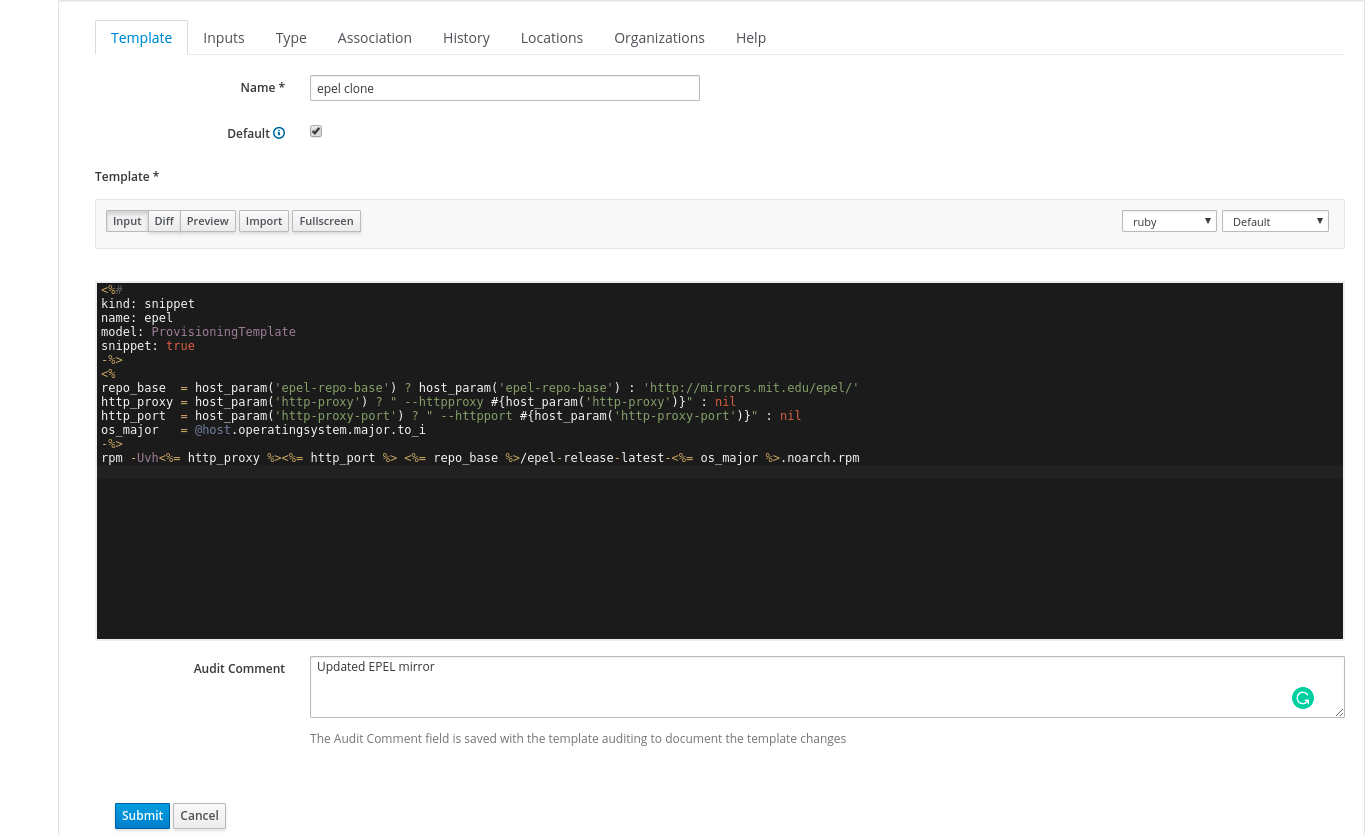
Submit to save the templateMonitor > AuditsPROVISIONING TEMPLATE epel clone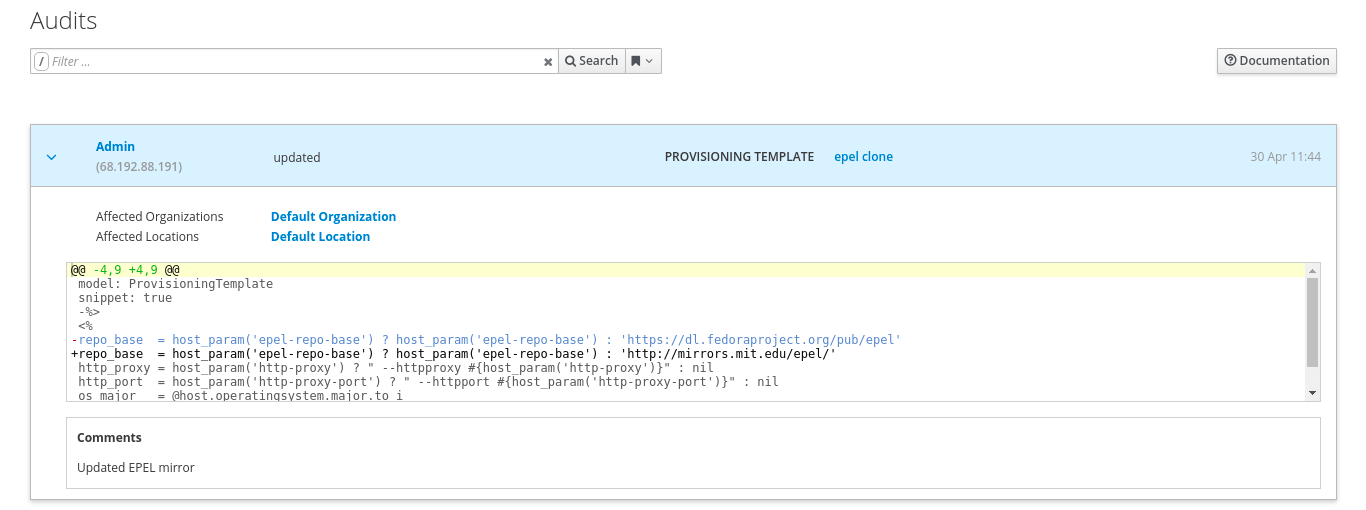
The following are stories that show off additional functionality in Satellite. These can be done if you still have time in the lab. If you choose to skip this section, feel free to go to the conclusion to view the community resources and other information.
Satellite 6.5 supports distributing custom content to Capsules and hosts via file repositories, which allows for a wide range of host workflows. The following section shows how to use Satellite 6.5 to distribute and deploy a versioned Tomcat application on host.
First create a product and a file repository to store the Java application content:
Content > ProductsCreate Product buttonName field enter Tomcat AppsSaveNew Repository buttonName field give it the name Hello Java AppType drop-down list select file (you can leave the rest of the fields as the default values)Save to save the repositoryThere is a pre-built WAR file on the Satellite that you can now upload to the file repository:
hammer repository upload-content --product "Tomcat Apps" \
--name "Hello Java App" \
--organization "Default Organization" \
--path /root/helloworld/hello.war
Hello Java AppContent Counts area, you will see one file listed1 to see that the hello.war file exists in that repository.Create a content view to make the application content accessible to Satellite hosts:
Content > Content ViewsCreate New View buttonHello World Application and click SaveFile Repositories tab and then click the Add sub-tabHello Java App from the list and click the Add Repositories buttonContent Views list by clicking the breadcrumb located under the Hello World Application titleNote in the Content Views List there is an existing content view called RHEL8 with errata that is used to distribute the OS content to hosts. On hosts where we will be deploying our Java application, we want to have also the OS content available. One way to ensure this is by creating a Composite Content View so that the application content is distributed together with the OS content:
Content Views page click the Create New View buttonHello World Application with RHEL8Composite View? and Auto Publish checkboxes and click SaveRHEL8 with errata and verify the version is set to Always Use LatestHello World Application and verify the version is set to Always Use LatestAdd Content ViewsYou have created a composite content view that is set to auto-publish whenever a component view is updated. Therefore, if the RHEL8 with errata Content View is re-published, or the application content view receives an update, the Composite Content View will publish a new version.
Hello World Application with RHEL8 page, click the arrow icons and select Hello World Application.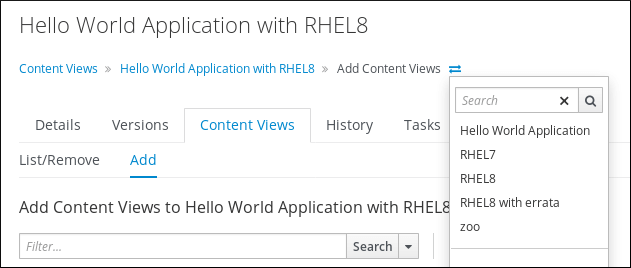
Publish New VersionSaveContent > Content Views and click Hello World Application with RHEL8Note that Version 1.0 is either published or still publishing via the Status column. If still publishing, wait until complete. Once complete, the Description column will show that this was due to an Auto Publish and which content view publish triggered the event.
To deploy the Java application we will use an Ansible playbook executed on host via remote execution. The playbook will start the Tomcat server and place the application content we published to the appropriate directory on host:
Hosts > All Hostsaqua.example.comSchedule Remote JobJob Category dropdown, select Ansible PlaybookSubmit. The Job Invocations view will be displayedaqua.example.com in the hosts tablehttp://aqua-<GUID>.rhpds.opentlc.com:8080/hello/web [Replace GUID in the URL with the GUID of your environment]Hello World! application is running, this is the application we just deployed with SatelliteOn the Satellite exists a newer version of our application in a pre-built WAR file at /root/hellosummit/hello.war. Knowing the steps from the previous excercise, can you re-deploy the application? (After successful re-deployment the application page should read Hello Red Hat Summit! at http://aqua-<GUID>.rhpds.opentlc.com:8080/hello/web)
Content views can be exported and imported from one organization to another, or from one Satellite to another. The Repositories contained in the Content View zoo have already been synced to Another Org, and the Content View has been created. We will import the version from Default Organization's Content View
Another OrgAnother Org.Content > Content Views and click zoo. Take note that versions of this Content View do not exist yetDefault OrganizationWe'll export the Default Organization's zoo Content View Version 5.0 to a file in order to prepare it for import to Another Org
zoo Content View in the Default Organizationhammer content-view version list --organization-id 1 --content-view zoo
--id option with the id 19hammer content-view version export --export-dir /var/lib/pulp/katello-export/ --id 19
/var/lib/pulp/katello-export/ that you can now import in to the Another Org organizationAnother OrgNow that we have the Content View Version exported, we can import it to Default Organization. The repositories in this Content View Version have already been synced for Another Org, this is required to import a Content View Version
Another Org organizationhammer organization list
Another Orghammer content-view version import --export-tar /var/lib/pulp/katello-export/export-zoo-19.tar \
--organization-id 3
zoo content view page in Another Org and notice the version has been imported!zoo content view into Another Org's zoo content view?Thanks for participating in the Hands on with Satellite 6.5 lab! We hope you enjoyed it and feel free to ask your lab administrators any questions you have about Satellite.
If you would like to keep up to date with the latest developments, or if you would like to submit a patch, please come find us in the community. The main communication area is the Foreman community, but you can of course participate in the Candlepin and Pulp communities as well.
#theforeman on freenode| Term | Definition |
|---|---|
| Activation Key | A registration macro which can be used in a kickstart file. These can be used to control actions at registration before Puppet Master kicks in. These are similar to Activation Keys in Red Hat Satellite 5, but they include less features. These features are covered by Puppet Manifests. |
| Ansible Playbook | Ansible playbook contains one or multiple plays. These plays defines the work to be done for a configuration on a managed node. Ansible plays are written in YAML. |
| Ansible Roles | Ansible Role is a set of tasks and additional files to configure a host. |
| Application Lifecycle Environment | Named areas where content can be moved to, and which systems are grouped into. Traditional usage of these are Dev -> Test -> Prod. Channel cloning was used for this in Red Hat Satellite 5 |
| Application Stream (AppStream) | The Application Stream repository provides content with varying life cycles as both modules and traditional packages for Red Hat Enterprise Linux 8. |
| Attach | Associating a Subscription to a Host which provides access to RPM content. |
| BaseOS | The BaseOS repository provides the core set of the Red Hat Enterprise Linux 8 content in the form of traditional RPM packages. |
| Capsule | A node in the Red Hat Satellite 6 deployment. It supports large scale deployments by providing services such as a Puppet Master, DHCP Integration, or a Content Cache (Pulp). |
| Common Vulnerability Exposure (CVE) | A standardized format for naming and reporting security exposures. It is maintained by the MITRE Corporation. |
| Compute Profile | Default attributes for new virtual machines on a compute resource. |
| Compute Resource | A virtual fabric, or cloud infrastructure, where hosts can be deployed by Red Hat Satellite 6. Examples include RHEV-M, OpenStack, EC2, and VMWare. |
| Content | Software packages (RPMS), or configuration modules. These are mirrored into the Library and then promoted into Application Lifecycle Environments to be used. |
| Content Delivery Network (CDN) | The mechanism to deliver Red Hat content in a geographically co-located fashion. For example, content which is synced by a Satellite 6 in Europe will pull content from a source in Europe. |
| Content View | A snapshot of content which is in the Library. Content views define the rules for creating the snapshots and a stream views created from the rules. Content Views are a refinement of channel cloning pattern from Red Hat Satellite 5. |
| Hammer | The name of the command line tool for Red Hat Satellite 6. It works like a standard cli as well as a shell in the same way that space-cmd works. |
| Host | A system, either physical or virtual, which is managed by Red Hat Satellite 6. |
| Host Group | A template for how a host should be built. This includes the packages to install, and the puppet classes to apply. |
| Image | A container which is currently not running. |
| Insights | A module providing access to selected Red Hat Customer Portal services from the Satellite web UI. |
| Location | A collection of default settings which represent a physical place. These can be nested so that a user can set up defaults for Europe, which are refined by Tel Aviv, which are refined by DataCenter East, and then finally by Rack 22. |
| Library | The Library is your collection of content which can be used. If you are an ITIL shop, it is your definitive software library. |
| Manifest | The means of transferring subscriptions from the Customer Portal to Red Hat Satellite 6. This is similar in function to satellite certificates. |
| Module | A Module describes a set of RPM packages that belong together. Modules can contain several Streams to make multiple versions of applications available for installation. |
| Module Streams | Module Streams hold different versions of the content within a Module. |
| Organization | A tenant in Red Hat Satellite 6. Organizations, or orgs, are collections of Hosts, Subscriptions, Users, and Application Lifecycle Environments. |
| Permission | The ability to perform an action. |
| Product | A collection of content repositories which are managed as a single unit. |
| Promote | The act of moving content from one Application Lifecycle Environment to another. |
| Provisioning Template | User defined templates for Kickstart files and other provisioning actions. These provide similar functionality as Kickstart Profiles and Snippets in Red Hat Satellite 5. |
| Puppet Agent | A Host agent which applies puppet changes to a Host. |
| Puppet Master | A component of a Capsule which provides puppet manifests to Hosts. |
| Repository | A collection of content (yum repository, containers, puppet repository). |
| Report Templates | Provide a way to generate custom text reports based on data from Red Hat Satellite 6.5. |
| Role | A collection of permissions which are applied to a set of resources (such as Hosts) |
| Smart Proxy | A component of a Capsule which can integrate with external services, such as DNS or DHCP. |
| Standard Operating Environment (SOE) | A controlled version of the operating system which applications are deployed on top of. |
| Subscription | The right to receive content and service for Red Hat. This is purchased by customers. |
| Subscription, Future-Dated | Subscriptions with Future dates into satellite allows an administrator to attach "noy-yet-valid" subscriptions to hosts, before their current subscription expire. |
| Syncing | The mirroring of content from external resources into the Red Hat Satellite 6 Library. |
| Sync Plans | Scheduled executing of syncing content. |
| System Purpose | A way to record the intended use of a Red Hat Enterprise Linux 8 system System. |
| Usergroup | A collection of roles which can be assigned to a collection of users. This is similar to the Role in Red Hat Satellite 5. |
| User | A human who works in Red Hat Satellite 6. Authentication and authorization can be done via built in logic, or using external LDAP or kerberos resources. |